Cyber Recovery Service

Experience a customized cyber recovery solution for your business. Benefit from a fully managed service and pristine data copies securely stored in an isolated digital vault. With this setup, you can instantly access clean data and restore your system post-cyberattacks.
Contact us now!Ensure modern protection and recovery for critical data, safeguarding against ransomware and other cyber threats
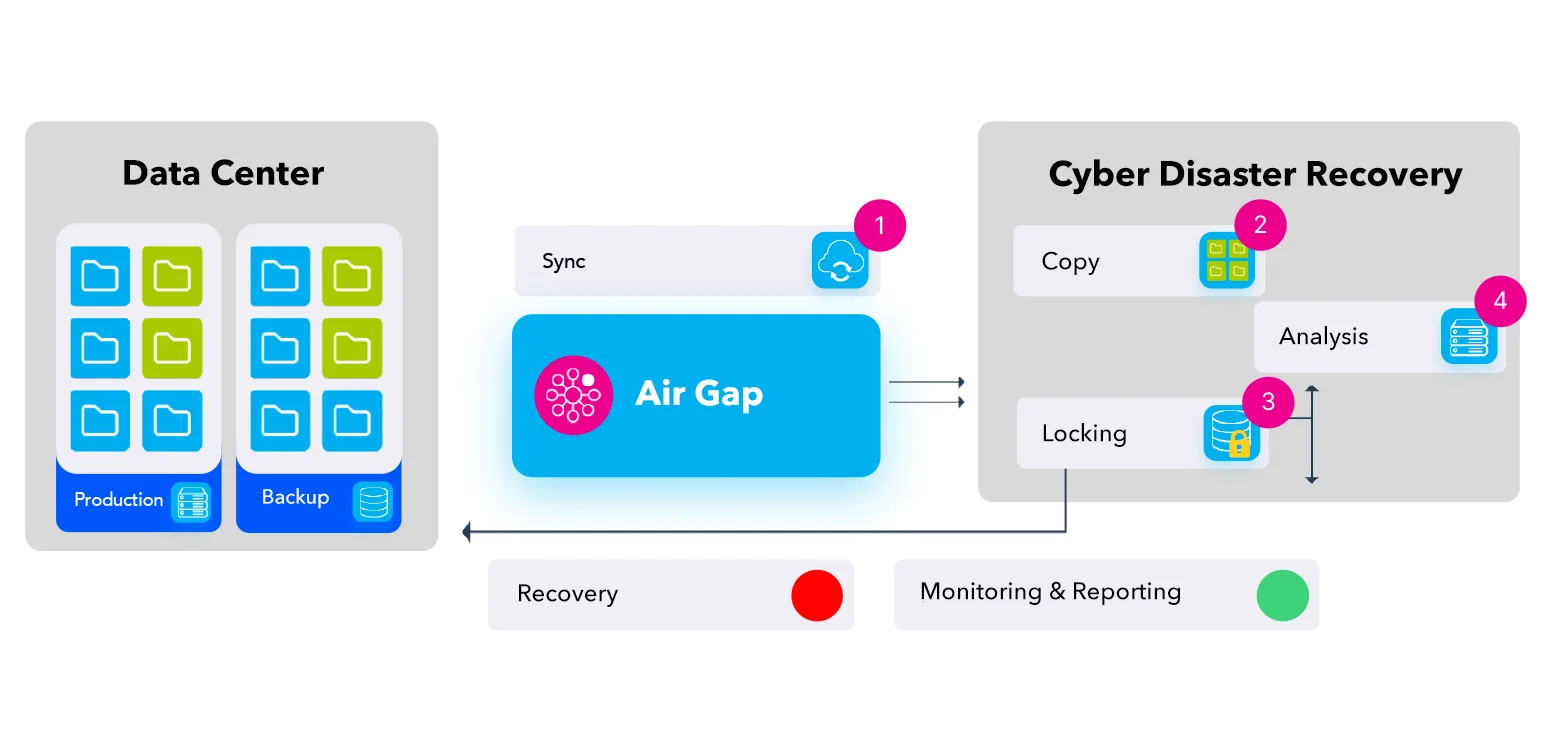
In today's business landscape, cyberattacks pose a constant threat to valuable data, potentially leading to financial losses and reputational damage. GlassHouse's PowerProtect Cyber Recovery Solution offers a state-of-the-art and intelligent defense mechanism to mitigate these risks promptly and recover your data efficiently. The CRS establishes a secure recovery vault that isolates critical data from the attacked environment, safeguarded in a physically isolated section accessible only through multi-factor authentication. Moreover, an automated operational air gap ensures network isolation and disables compromised management interfaces.
PowerProtect CRS streamlines the synchronization between production systems and the vault, ensuring that copied data remains unalterable through key protection policies. In the event of a cyberattack, you can quickly identify and access clean data copies to restore critical systems and resume business operations. The CyberSense software employs Machine Learning to detect corrupted data infiltrated by ransomware attacks within the data center, achieving a 99.5% effectiveness rate by analyzing content-focused parameters. These operations are carried out within the secure environment of the air-gapped vault. The data recovery and remediation workflows guarantee the rapid and reliable restoration of business-critical systems with PowerProtect CRS. Businesses leveraging the Cyber Recovery Service benefit from automated recovery features executed directly within the isolated vault.
Following the setup of your Cyber Recovery infrastructure, we collaborate to identify and prioritize critical systems requiring protection. Through data analysis, technology assessment, and recovery requirement definition, we tailor solutions to your specific needs. Leveraging our extensive expertise and the Dell PowerProtect-based Cyber Recovery service, we empower you to swiftly identify solid data and restore it securely.
Complete the form to get in touch with us! Let's build the infrastructure of success for your IT operations together.
Discover the features of our Cyber Recovery Service
Unveil the benefits of our Cyber Recovery Service!

Protect your critical data at the highest level, securing it against cyberattacks.
Reduce the burden on IT staff and prevent insider threats with a fully managed service.
Quickly restart your workflow by accessing offline, air-gapped 'golden' copies.
Protect against the costs of attacks and potential data loss by maintaining an air-gapped, immutable copy.
Ensure business continuity by rapidly restoring affected systems and services.
Blog content that may be of interest to you
Frequently Asked Questions
The CRS architecture is designed to operate in full alignment with Dell Data Domain’s DD Boost protocol and its advanced deduplication and security features. This ensures that all data is transmitted, stored, and optimized securely end-to-end. In line with security policies, performance requirements, and operational standards, only Data Domain infrastructure is deployed within the CRS scope.
It is not mandatory; however, for a fully comprehensive CRS architecture, we recommend deploying the components in separate cabinets.
As long as your license subscription remains active, you can access all updates. If you prefer to perform upgrades without internet connectivity, Dell Technologies provides a USB device through which package upgrades can be installed.
One of the core advantages of this solution is the CyberSense AI-driven analytics technology. To fully benefit from advanced cyber-resilience and AI-based anomaly detection (e.g., CyberSense), your DD appliance must be a supported and current model approved by the manufacturer.
DR solutions ensure business continuity by maintaining redundant copies of data in a secondary location. However, traditional DR architectures do not include advanced cyber-resilience mechanisms such as air-gap isolation or anomaly detection. As a result, in ransomware scenarios, the replicated backups may still be compromised.
CRS takes DR one step further. Backups are stored in an isolated Cyber Vault environment (air-gapped). CyberSense analyzes backup data for corruption, encryption attempts, or abnormal behavior. This ensures that only clean and verified datasets are restored.
In short: DR guarantees the presence of a backup; CRS guarantees the backup is clean and trustworthy. This approach prevents long periods of uncertainty during an attack and enables rapid restoration using data proven to be uncompromised.
CRS is fully compatible with all backup software within the Dell Technologies ecosystem (Avamar, PowerProtect Data Manager, NetWorker, etc.). It also supports widely used enterprise backup solutions such as Commvault and Veritas NetBackup.
We provide Runbook documentation in both Turkish and English. Likewise, High Level Design (HLD) and Low Level Design (LLD) documents are also delivered in both languages.
CRS supports only backups taken on Dell Technologies PowerProtect Data Domain within its protection layer. When Oracle databases are protected via Data Domain AppDirect integration or Dell backup software such as Avamar / NetWorker, CyberSense analysis is applied. This analysis identifies suspicious changes, user/password modifications, anomaly behavior, or potential corruption, and alerts are generated automatically.
No. Even if you already have a Data Domain system, adding another unit is not sufficient to deploy CRS. The Cyber Recovery architecture also requires additional servers for hosting the Cyber Recovery Application, CyberSense, and management components, as well as the creation of an isolated and secure Cyber Vault environment.
Yes. CyberSense licensing is based on the raw data capacity, not on post-deduplication or post-compression size. For example, even if 100 TB of data is reduced to 20 TB on Data Domain, the license calculation is still based on 100 TB.
Yes, a firewall can be used instead of a Data Diode; however, there are architectural differences.
A Data Diode provides strictly one-way communication (from internal to external), minimizing the attack surface of the Cyber Recovery environment and allowing only SNMP, email, or Syslog alerts.
A firewall manages bidirectional traffic; if not configured properly, the exposure surface increases significantly. Therefore, very strict access controls are essential in firewall-based scenarios.
A separate NTP device is not mandatory. A local NTP configuration can be used within the Cyber Recovery environment. However, some organizations choose specialized solutions such as satellite-based NTP appliances for high-accuracy, independent time synchronization.
Yes. There is an interface/admin panel that displays license consumption and remaining capacity. In the latest versions, capacity usage is presented visually, making license tracking and capacity planning significantly easier.
Yes, we provide this service for customers operating on GlassHouse Cloud. However, the servers must also run in GH Cloud. While it is technically possible to deploy the architecture in public clouds such as AWS or Azure, it is not recommended. Key challenges include:
High network bandwidth requirements for replication, increasing cost
Significant disk, RAM, and CPU consumption due to indexing and analytics processes
More complex access control when applying air-gap principles
For these reasons, the most effective and cost-efficient deployment model for cloud-hosted CRS is on GlassHouse Cloud.