3 Reasons to use PowerProtect with Cyber Recovery Services
In a data-driven world irrespective of industry and geography, data has become a currency and invaluable to organizations. Organizations are researching the right level of data protection. Protecting “keys of your kingdom” your critical applications to the organization.Understanding the Ecosystem || Deep Dive into the CRS
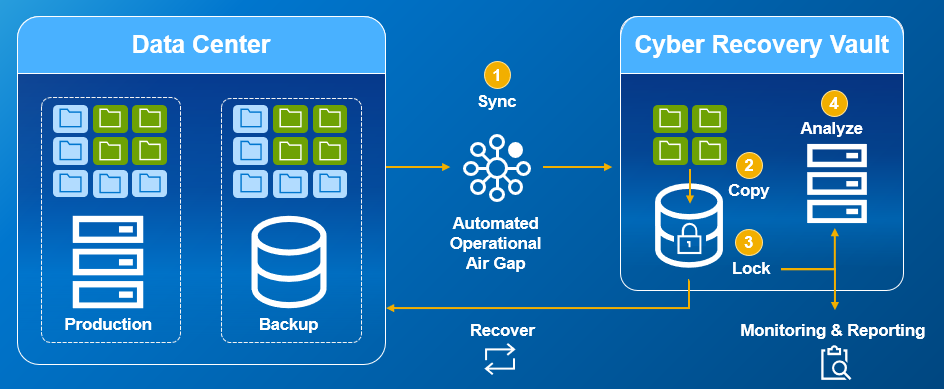
In a digital evolution, I see customers moving away from the traditional protection methods to be agile with the business transformation. i.e., moving from tape systems to a multi-disk system, with a lower TCO (total cost of ownership) and RPO (recovery point objective) as well as syncing data copies between sites. If a cybercrime occurs and takes control of your data (storage) or datasets (protection copies), you are required to have critical data in an offline state/site.
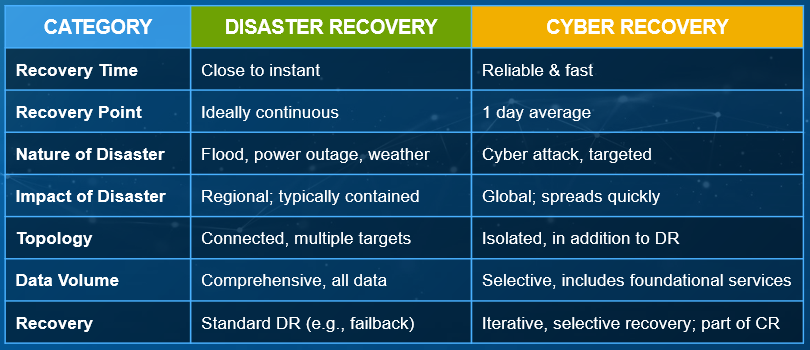
Disaster recovery (DR) has a purpose for daily operations: get your business back up and running with minimal impact. Cyber Recovery is based on your STO (Survival Time Objection) ensuring how quick to recovery after an attack.
What the research shows
69% of organizations lack the confidence that they could recover business-critical applications in an event of a cyber-attack i.e., how to identify if data has not been infected, how to recover after a cyber-attack and the time to assess the destruction. A cyber-attack occurs every 11 seconds, according to Accenture's forecast $6T worth data risk in 2021 and Cyber Magazine predicting that Cybercrime to cost $10.5T by 2025. How PowerProtect can help you
PowerProtect Cyber Recovery protects and isolates critical data from ransomware and other sophisticated threats. Machine learning identifies suspicious activity and allows you to recover known good data and resume normal business operations with confidence.
How does it work?
- • Operational Automated air gap with data isolation and immutability
- • CyberSense analytics and Machine Learning monitor data integrity
- • Accelerate cyber and ransomware attack data recovery
Why you should implement Cyber Recovery using GlassHouse
GlassHouse aims to make this process easy for customers using our extensive experience and skill to provide for the most efficient implementation. Our culture at GlassHouse is built on a tenant of service for leading enterprises, especially those with the most demanding business continuity needs. GlassHouse is about providing support to customers in their digitalization journey using their deep technical expertise; Managed Cloud, Security Services, SAP Infrastructure Service and Business Continuity Services. Data is the most valuable asset in the new economy.
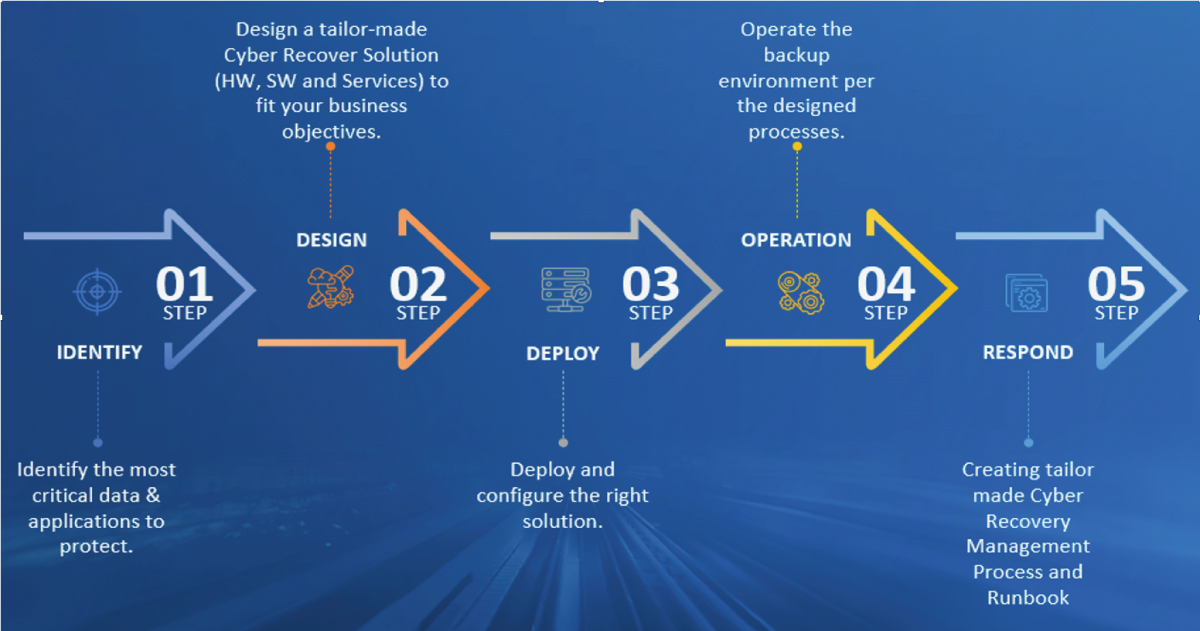
GlassHouse can tailor a Cyber Recovery Solution in 5 easy steps:
For a free Cyber Recovery assessment, do not hesitate to contact GlassHouse.
You can also take a look at "Managed Backup Services"
Author: Zaheer Haniff, Data Protection and Cyber Recovery Specialist at Dell Technologies.